As industrial environments grow more connected, the boundary between the shop floor and the internet grows dangerously thin. Network segmentation is no longer optional — it is the foundational architecture that keeps operational technology alive.
In the summer of 2021, a water treatment facility in Oldsmar, Florida, was remotely accessed by an unknown attacker who briefly raised the sodium hydroxide concentration to 111 times the acceptable level. Only a vigilant operator caught the change in time. The system was connected. It was not segmented. These two facts were the difference between a near-miss and a mass-casualty event.
This incident is not a footnote it is a warning sign emblazoned across every industrial facility that still treats its operational technology (OT) network as an afterthought. Today, as manufacturing plants, power grids, water utilities, and oil pipelines accelerate their digital transformation journeys, the question of network segmentation sits squarely at the intersection of productivity and survival.
73%
of OT organizations experienced a cyberattack in 2023
$4.5M
Average cost of an industrial data breach
300%
Increase in ICS-targeted malware since 2020
What Is Network Segmentation and Why Does It Matter in Industrial Environments?
Network segmentation is the practice of dividing a computer network into smaller, isolated subnetworks called segments or zones to control the flow of traffic between them.
In enterprise IT environments, segmentation is a well-established security best practice. In industrial control system (ICS) and operational technology (OT) environments, it is both more complex and more critical.
Industrial systems govern physical processes: turbines spinning, valves opening, conveyor belts moving, chillers cooling. A cyberattack that disrupts an enterprise email server is painful.
A cyberattack that triggers an unexpected shutdown of a chemical reactor or tampers with a power grid frequency is potentially fatal. This physical consequence of a digital breach is what makes OT cybersecurity its own discipline and network segmentation its cornerstone strategy.
Key insight: Unlike IT networks, where availability can sometimes be sacrificed for security, OT networks must maintain near-100% uptime. Segmentation must be designed so that security controls never introduce latency or failure points into time-sensitive industrial processes.
The Purdue Model: A Blueprint for Industrial Network Architecture
For decades, the Purdue Enterprise Reference Architecture has provided the foundational model for structuring industrial networks in layers. While modern cloud and edge computing have pushed the model’s boundaries, it remains the most widely understood framework for OT network design.
The Purdue model organizes industrial systems into five hierarchical levels, each with a distinct function and security posture:
| Level | Name | Description | Key Components |
| Level 4/5 | Enterprise Zone | The corporate network where business systems reside. | ERP systems, Email, Internet access. |
| Level 3.5 | DMZ | The “buffer” zone that prevents direct IT-to-OT talk. | Proxy servers, Patch management (WSUS). |
| Level 3 | Operations Systems | Site-wide control and monitoring. | Historians, Asset management, HMIs. |
| Level 2 | Control Level | Where the “thinking” happens for specific cells. | PLCs, SCADA software, Operator consoles. |
| Level 1 | Basic Control | Direct sensing and manipulation of the process. | Variable Frequency Drives (VFDs), Sensors. |
| Level 0 | Process | The physical equipment. | Motors, Valves, Actuators. |
Effective segmentation creates strict boundaries between each level, ensuring that a compromise at Level 4 (a phishing attack on a corporate workstation, for example) cannot propagate down to Level 1 PLCs controlling a physical process. Traffic between levels should be explicitly defined, minimized, and monitored never assumed safe.
Core Techniques for Industrial Network Segmentation
1. Firewalls and Industrial DMZs
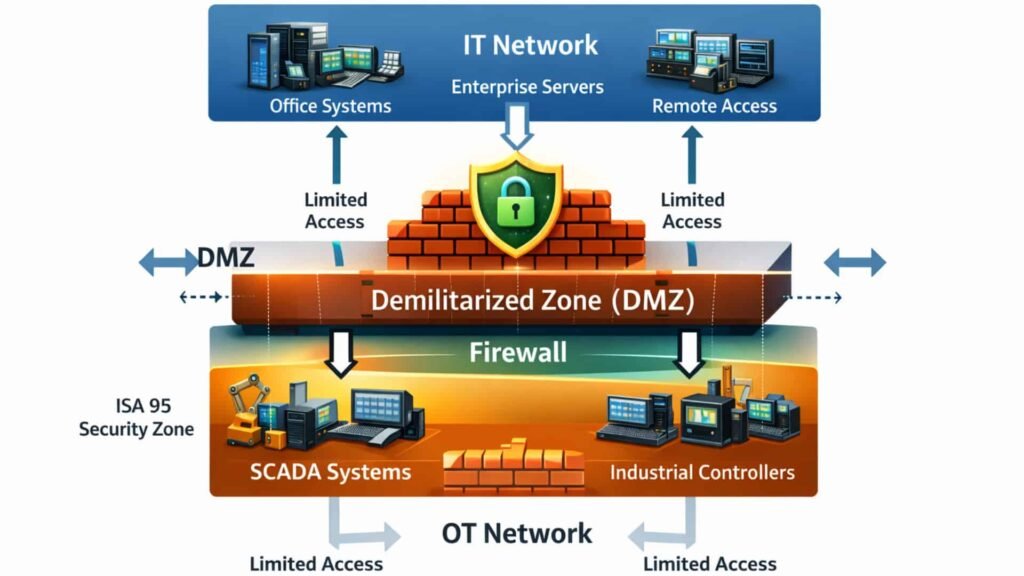
The industrial DMZ is the most critical segmentation boundary in any OT architecture. Positioned between the OT network (Level 3 and below) and the corporate IT network (Level 4 and above), the DMZ hosts data historians, file transfer servers, and jump hosts that allow controlled, audited data exchange without creating a direct path between the two network worlds. Industrial-grade firewalls with OT-protocol awareness supporting Modbus, DNP3, EtherNet/IP, and Profinet enforce policy at the application layer, not just the port level.
2. VLANs and Microsegmentation
Virtual Local Area Networks (VLANs) allow physical network infrastructure to be logically partitioned, isolating different device groups — HMIs, engineering workstations, historian servers, and field controllers even when they share the same physical switches. For higher-security environments, microsegmentation extends this concept further, applying granular access control policies at the individual device or workload level. In ICS environments where east-west lateral movement is a primary attack vector, microsegmentation is an increasingly important control.
3. Unidirectional Security Gateways
Also known as data diodes, unidirectional gateways use optical hardware to enforce one-way data flows most commonly from OT systems outward to IT or historian systems. Because data physically cannot travel back across the fiber link, even a fully compromised IT network cannot send commands or malware back into the OT environment. Data diodes are widely deployed in nuclear power stations, water utilities, and critical national infrastructure where the regulatory and safety consequences of bidirectional compromise are unacceptable.
4. Network Access Control (NAC)
Industrial facilities increasingly contend with a sprawling asset inventory: legacy PLCs from the 1990s, modern IIoT sensors, contractor laptops, wireless gateways, and industrial tablets all sharing the same physical infrastructure. NAC solutions authenticate and profile devices before granting network access, ensuring that unknown or non-compliant assets are quarantined rather than admitted freely. Asset visibility is a prerequisite for effective segmentation you cannot protect what you cannot see.
The Convergence Challenge: IT/OT and the IIoT Explosion
The traditional air gap between IT and OT is, in most organizations, a comfortable fiction. Industry 4.0 — the fourth industrial revolution — has fundamentally changed the connectivity model of industrial environments. Cloud-connected SCADA systems, remote vendor access, IIoT sensor arrays streaming telemetry to cloud analytics platforms, and digital twin technologies all require bidirectional connectivity that the Purdue model was not designed to accommodate.
This convergence creates new segmentation challenges that demand modern architectural responses:
- Legacy OT devices were designed for reliability, not security. Many PLCs and RTUs run decades-old firmware with no authentication, no encryption, and no patch capability. Segmentation must compensate for what the device itself cannot provide.
- Remote access for vendor support and remote operations creates persistent connection pathways that, if not rigorously controlled, become persistent attack surfaces. Privileged Access Workstations (PAWs) and jump servers in the DMZ, with multi-factor authentication and session recording, are essential controls.
- Cloud integration for analytics, predictive maintenance, and digital twins requires data to flow from deep inside the OT network to external cloud platforms. Secure data pipelines with strict egress filtering and certificate-based authentication are required to prevent this connection from becoming a bidirectional attack path.
- IIoT proliferation places thousands of new, often resource-constrained devices onto OT networks. Many lack the processing headroom to run endpoint security agents, placing the entire security burden on the network architecture — precisely where segmentation and network-level monitoring must compensate.
Standards and Frameworks That Govern OT Segmentation
Regulators and standards bodies have recognized the segmentation imperative. Several frameworks now provide detailed, mandatory, or recommended guidance on industrial network architecture:
IEC 62443 is the definitive international standard for industrial cybersecurity, introducing the concept of Security Levels (SL 1–4) and Zones and Conduits a formalized methodology for defining network segments and the controlled pathways between them. Compliance with IEC 62443 is increasingly required by industrial asset owners in energy, manufacturing, and process industries worldwide.
NERC CIP (North American Electric Reliability Corporation Critical Infrastructure Protection standards) mandates electronic security perimeters, access management, and monitoring requirements for the bulk electric system in North America effectively codifying segmentation requirements for power grid operators.
NIST SP 800-82 provides comprehensive guidance on securing industrial control systems, including network architecture recommendations aligned with the Purdue model and practical segmentation controls applicable across industrial sectors.
ISA/IEC 62443-3-3 defines system-level security requirements and specifically addresses the implementation of security zones and conduits the building blocks of any properly segmented OT network.
